Installation of the Fabasoft Folio Portlet
This chapter describes the installation of the Fabasoft Folio Portlet.
Installation and Configuration of Liferay Portal
Liferay Portal comes in a bundle with Apache Tomcat. You can download the package from http://www.liferay.com: new window. You also can find additional information about how to install and configure the Liferay Portal at this web site.
Cluster Configuration
A description how to set up an Apache Tomcat cluster environment can be found here:
http://tomcat.apache.org/tomcat-8.0-doc/cluster-howto.html: new window
Installation of the Fabasoft Folio Portlet
To install the Fabasoft Folio Portlet perform the following steps.
- Run the Fabasoft Server Setup on the server where the Fabasoft Folio eService is installed or should be installed.
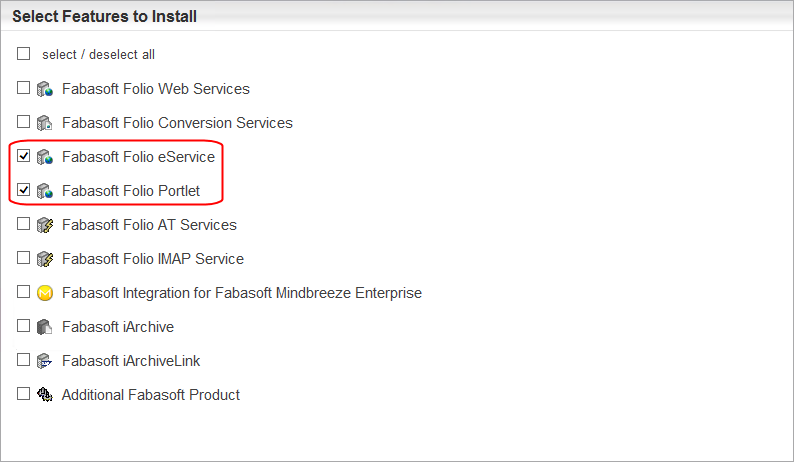
- Select the feature “Fabasoft Folio Portlet”. If you do not have installed a Fabasoft Folio eService so far select this service too. Click “Next”.
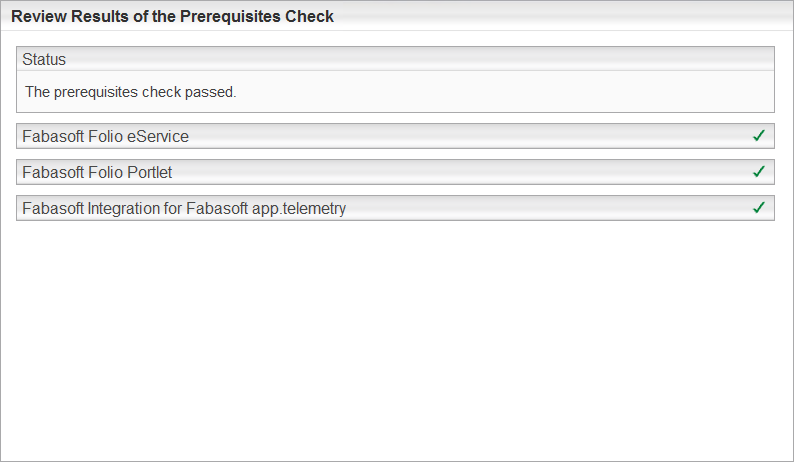
- If all required software is installed, the prerequisites check reports no missing tools.
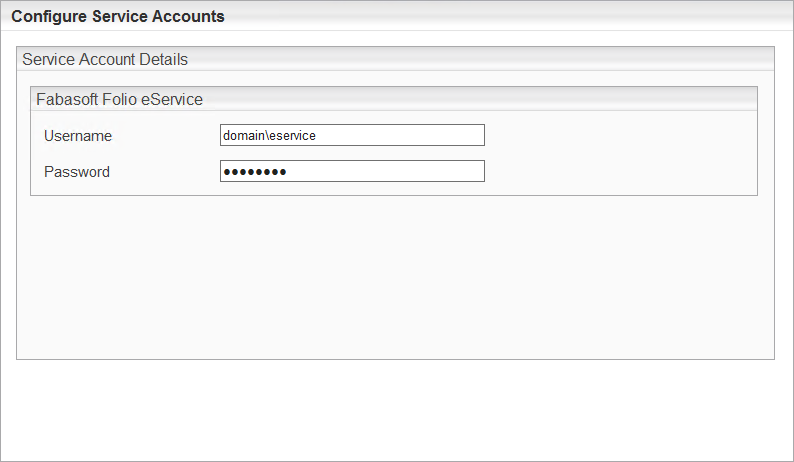
- Specify an account which is used to run the Fabasoft Folio eService.
- On the summary page in the Fabasoft Folio eService area click “Edit” to define the parameters. Afterwards click “OK”.
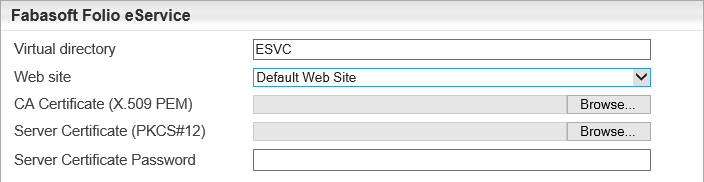
- Virtual Directory
Define the name of the virtual directory for the Fabasoft Folio eService. This value is needed at the Folio Portlet configuration. Ensure that this value meets the settings of the Folio Portlet parameters. - Web Site
Defines the web site where the Fabasoft Folio eService runs. - CA Certificate (X.509 PEM)
If own certificates are used select your CA here. - Server Certificate (PKCS#12)
Select the certificate for the web server here. - Server Certificate Password
Type the password for the server certificate here.
Note: If you want that the eService Setup generates the CA and server certificate leave these three fields blank.
- Virtual Directory
- On the summary page in the Fabasoft Folio Portlet area click “Edit” to define the parameters. Afterwards click “OK”.
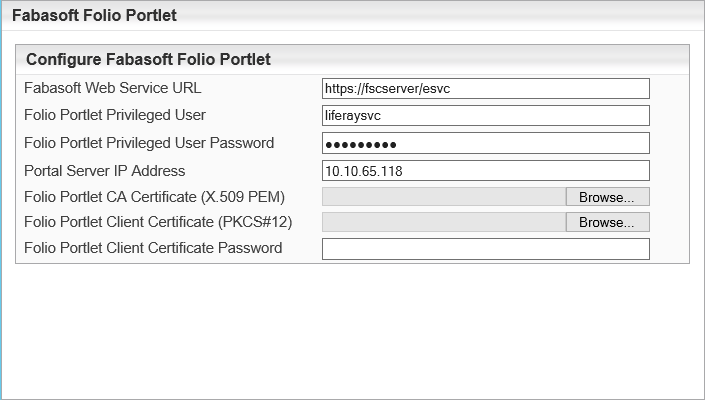
- Fabasoft Web Service URL
Specifies the URL to the Fabasoft Folio eService.
Note: The web service must be reachable over HTTPS using a certificate. A not encrypted connection is not accepted by the Fabasoft Folio Web Service. If the certificates should be generated automatically by the Fabasoft server setup define the fully qualified domain name (FQDN) here, otherwise a connection would fail due to a certificate error. - Folio Portlet Privileged User
Specify a username which is used by the Folio Portlet to authenticate at Fabasoft. The Fabasoft server setup creates a user in the Fabasoft Folio Domain having this userlogname. This user is defined as privileged user. On a Microsoft Windows platform this user must exist on the web server.
Note: If the user does not exist as an operating system user the Fabasoft setup will create a local user automatically on Microsoft Windows platforms. - Folio Portlet Privileged User Password
Specify the password of the Folio Portlet Privileged User. This parameter has to be specified only on Microsoft Windows platforms. Default value: Password1 - Portal Server IP Address
Specify the IP address or CIDR range of the server where the portal server is installed. If the portal server and the Fabasoft Folio eService are installed on the same server specify “127.0.0.1” on Linux or the hosts IP address (e.g. "10.10.x.x") on Microsoft Windows servers. To allow access from a subnet specify a CDIR range (e.g. 10.10.0.0/16). This IP address is necessary to ensure the security with remote user authentication. - Folio Portlet Client Certificate (PKCS#12)
If own certificates are used select your client certificate here which the portal server uses to authenticate at the Fabasoft Folio eService.
Note: The login name of the Folio Portlet Privileged User has to be identical to the common name of the used client certificate for this user. In some cases this login name has to be added manually. See also chapter “ Portal Service User”. - Folio Portlet Client Certificate Password
Type the appropriate password for the client certificate. - Folio Portlet CA Certificate (X.509 PEM)
Select your CA.
Note: If you want that the Folio Portlet Setup generates the client certificate leave these three fields blank.
If an existing SSL web service is used the certificates must be set here anyway. The SSL connection must be set as it requires client certificates and a mapping of the client certificate to the user must be configured.
- Fabasoft Web Service URL
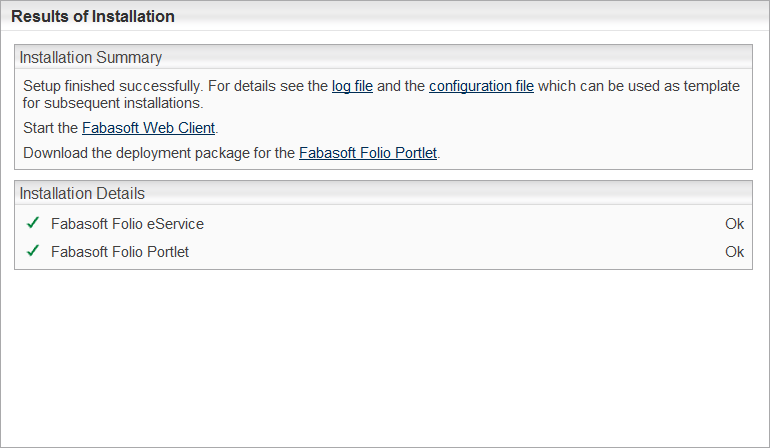
- After all parameters are set click “Install”.
- After the Fabasoft Server setup has finished there is a Link to the Fabasoft Folio Portlet deployment package. So you can store the kit to a specific directory. By default it is stored in C:\Program Files\Fabasoft\Components\Setup\Folio Portlet\ on Microsoft Windows and in /var/opt/fabasoft/folioportlet/ on Linux.
- Extract the package on local directory on the server hosting the Apache Tomcat server.
- Stop the Apache Tomcat server.
- Open a command line and switch to the deployment directory. It is important to switch to the deployment directory because otherwise the scripts will not be able to find some necessary files.
- Run the Fabasoft Folio Portlet deploy script (portletdeploy.bat file on Microsoft Windows, portletdeploy.sh -i on Linux).
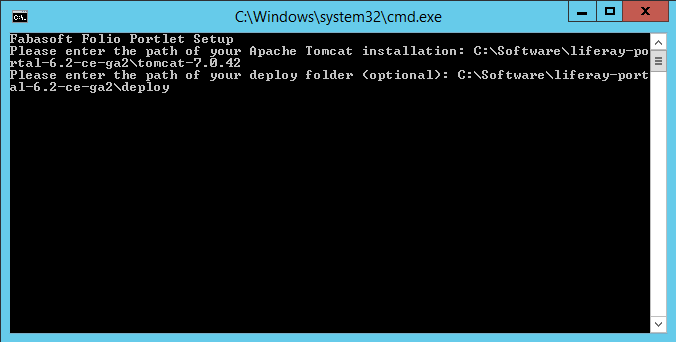
The deployment script prompts the user for the path to the Apache Tomcat installation. Specify the full path to the Apache Tomcat server’s root directory.
Furthermore the deploy directory can be specified to deploy the Fabasoft Folio Portlet automatically when Apache Tomcat server is started. If this parameter is not specified the Fabasoft Folio Portlet in the Portlets subdirectory relatively to the deployment scripts can be used to deploy the portlet.
Note:- The -Dsun.security.ssl.allowUnsafeRenegotiation=true parameter is added to the JAVA_OPTS variable of Apache Tomcat.
- Start the Apache Tomcat server.
Note: If a user with the given login name already exists, no new service user object is created. Verify that the service user in Fabasoft has got his default role as Portal Service User.
Note: When using TLS 1.3 with Internet Information Services (IIS), the client needs to support post-handshake authentication.